Introduction
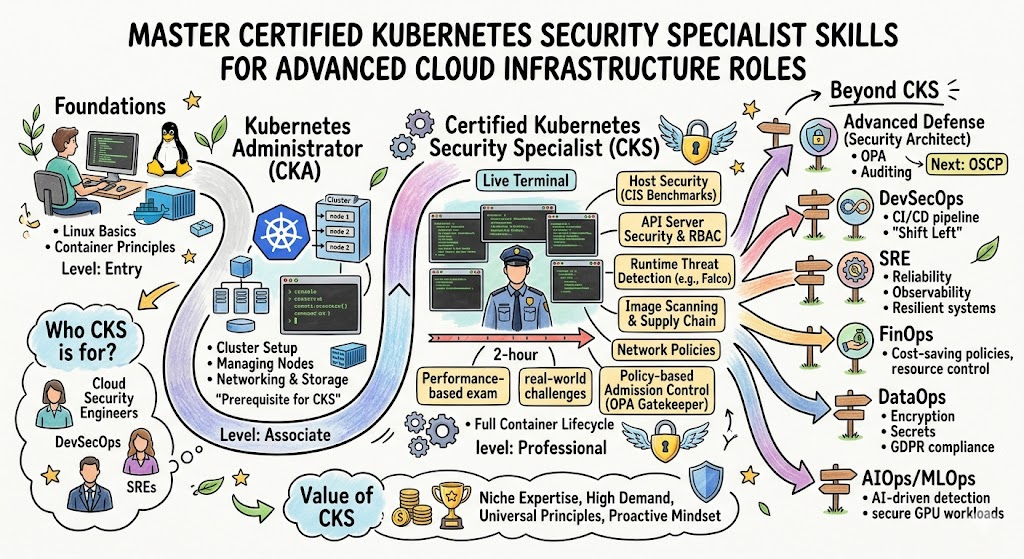
Security remains the most critical frontier in the modern cloud-native landscape for every engineering team. Professionals who master the Certified Kubernetes Security Specialist (CKS) Certification Training Course gain the precise skills needed to protect high-stakes production environments. This comprehensive roadmap helps engineers navigate the complexities of container hardening and threat mitigation through expert guidance at DevOpsSchool. By following this structured path, technical leaders ensure their infrastructure survives the evolving landscape of cyber threats while maintaining operational excellence.
What is the Certified Kubernetes Security Specialist (CKS) Certification Training Course?
The Certified Kubernetes Security Specialist (CKS) Certification Training Course functions as a rigorous, performance-based validation of an engineer’s ability to secure a cloud-native stack. It transcends basic administration by focusing on the entire lifecycle of a container, from the initial build to the active runtime phase. Organizations rely on this curriculum to establish a baseline of security competence that moves beyond theoretical knowledge into practical, verifiable command-line expertise.
Every module within this program mirrors the challenges that site reliability engineers face in real-world enterprise clusters. It forces practitioners to confront vulnerabilities in the supply chain, misconfigured API servers, and insecure pod definitions. By successfully navigating this course, professionals prove they can implement a “Defense in Depth” strategy that protects sensitive data and maintains service availability. This certification serves as the industry’s most respected benchmark for cloud-native security excellence.
Who Should Pursue Certified Kubernetes Security Specialist (CKS) Certification Training Course?
Senior DevOps engineers and security architects who already possess a foundational grasp of cluster management represent the primary audience for this credential. Since the program demands a valid CKA as a prerequisite, it specifically targets those ready to move into advanced DevSecOps roles. Engineering managers often encourage their lead platform engineers to take this course to ensure the internal developer platform meets strict compliance standards.
Security professionals transitioning from traditional networking to the cloud-native world find this certification indispensable for understanding container-specific threats. In the Indian tech market and global hubs, recruiters prioritize candidates who can demonstrate these specific hardening skills during technical interviews. Whether you manage a small startup stack or a massive multi-region enterprise environment, this training provides the specialized knowledge required to safeguard digital assets.
Why Certified Kubernetes Security Specialist (CKS) Certification Training Course is Valuable
Enterprises across the globe currently face a massive shortage of talent capable of securing automated orchestration platforms. Earning this certification places an engineer in the top tier of the workforce, directly impacting salary potential and career longevity. Unlike general security certificates, the CKS focuses on the high-demand niche of Kubernetes, which currently powers the majority of modern enterprise applications.
The value extends beyond a simple badge; it provides a framework for reducing the attack surface of production infrastructure. Professionals learn to automate security checks, which prevents costly manual errors and reduces the likelihood of catastrophic data breaches. This investment of time and energy yields a significant return by making an individual a critical asset in any organization’s risk management strategy.
Certified Kubernetes Security Specialist (CKS) Certification Training Course Overview
Candidates access this specialized program via the Certified Kubernetes Security Specialist (CKS) Certification Training Course hosted by DevOpsSchool. The exam environment strictly tests hands-on ability through a two-hour session where engineers solve complex security scenarios in real-time. The Cloud Native Computing Foundation maintains the syllabus to ensure it reflects the latest security patches and community best practices.
The structure of the assessment emphasizes six core domains, ranging from cluster setup to system hardening and runtime protection. This practical approach ensures that every certified individual can actually perform the tasks required in a production setting. By focusing on performance rather than memorization, the program maintains its integrity as a high-value credential for the engineering community.
Certified Kubernetes Security Specialist (CKS) Certification Training Course Tracks & Levels
The ecosystem offers a clear progression path that starts with basic cloud awareness before moving into deep technical specialization. Most engineers begin at the foundational level to understand the broader landscape of CNCF projects and container standards. From there, they advance through the associate administrative level to gain the operational experience necessary for security-focused studies.
The specialty track, where the CKS resides, represents the pinnacle of technical achievement for infrastructure defenders. This level aligns perfectly with senior-grade career roles that demand high levels of autonomy and architectural decision-making power. By following this tiered structure, a professional builds a comprehensive skill set that covers every aspect of the modern software delivery lifecycle.
Complete Certified Kubernetes Security Specialist (CKS) Certification Training Course Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| Cloud Literacy | Foundational | Managers & Freshers | None | Ecosystem Terms | 1st |
| Operations | Associate | DevOps Engineers | IT Basics | Cluster Management | 2nd |
| Security | Specialty | DevSecOps Experts | Valid CKA | Hardening & Audit | 3rd |
| Development | Associate | App Developers | Coding Knowledge | Secure Pod Design | Optional |
Detailed Guide for Each Certified Kubernetes Security Specialist (CKS) Certification Training Course
Foundational Level
Certified Kubernetes Security Specialist (CKS) Certification Training Course – KCNA
What it is
The KCNA serves as an entry point into the world of Kubernetes and cloud-native technologies. It confirms that a person understands the basic concepts of orchestration, observability, and application delivery.
Who should take it
Aspiring cloud engineers and project managers who need a solid conceptual foundation should start here. It provides the vocabulary and high-level understanding required to collaborate with technical teams effectively.
Skills you’ll gain
- Identifying core Kubernetes components and their functions.
- Understanding the role of the CNCF and its hosted projects.
- Grasping the basics of containerization and microservices.
- Learning about cloud-native monitoring and logging architectures.
Real-world projects you should be able to do
- Describe the architectural requirements for a simple cloud-native app.
- Explain the benefits of container orchestration to non-technical stakeholders.
Preparation plan
- 7 Days: Review official CNCF glossaries and watch introductory architecture videos.
- 30 Days: Complete a foundational course and pass multiple mock quizzes.
- 60 Days: Focus on reading whitepapers regarding cloud-native security and observability.
Common mistakes
- Focusing too much on YAML syntax instead of conceptual architecture.
- Neglecting the non-Kubernetes projects within the CNCF landscape.
Best next certification after this
- Same-track option: CKA (Certified Kubernetes Administrator).
- Cross-track option: PCA (Prometheus Certified Associate).
- Leadership option: Cloud Digital Leader.
Associate Level
Certified Kubernetes Security Specialist (CKS) Certification Training Course – CKA
What it is
The CKA validates the core administrative skills needed to run a production-ready Kubernetes cluster. It focuses on installation, networking, and the basic security configurations required for daily operations.
Who should take it
System administrators and DevOps practitioners who want to prove their operational competence take this exam. It acts as the gatekeeper for all advanced Kubernetes certifications.
Skills you’ll gain
- Building and configuring clusters using the kubeadm tool.
- Troubleshooting complex networking and pod communication issues.
- Managing cluster storage and persistent volumes effectively.
- Implementing basic RBAC and resource quotas for namespaces.
Real-world projects you should be able to do
- Provision a high-availability Kubernetes cluster from scratch.
- Diagnose and fix a broken control plane component in real-time.
Preparation plan
- 7 Days: Practice imperative commands and cluster troubleshooting scenarios daily.
- 30 Days: Work through a comprehensive lab-based course with multiple mock exams.
- 60 Days: Build various cluster configurations on local hardware or cloud VMs.
Common mistakes
- Relying on GUI tools instead of mastering the kubectl command line.
- Failing to practice the manual installation of cluster components.
Best next certification after this
- Same-track option: CKS (Certified Kubernetes Security Specialist).
- Cross-track option: CKAD (Certified Kubernetes Application Developer).
- Leadership option: DevOps Lead Professional.
Professional/Specialty Level
Certified Kubernetes Security Specialist (CKS) Certification Training Course – CKS
What it is
The CKS represents the most advanced security credential for Kubernetes practitioners. It focuses on the specific tools and techniques used to harden clusters and monitor them for active threats.
Who should take it
Current CKA holders who want to specialize in DevSecOps or cloud security engineering should pursue this. It is ideal for those responsible for protecting sensitive workloads in production.
Skills you’ll gain
- Securing the container image supply chain and scanning for flaws.
- Configuring admission controllers to enforce strict security policies.
- Hardening the underlying host OS and the Kubernetes API server.
- Setting up runtime security monitoring with tools like Falco.
Real-world projects you should be able to do
- Implement a full-stack security audit for a multi-tenant cluster.
- Block unauthorized system calls using Seccomp and AppArmor profiles.
Preparation plan
- 7 Days: Focus exclusively on third-party security tools like Trivy and Falco.
- 30 Days: Complete several full-length practice exams on platforms like Killer.sh.
- 60 Days: Build a “broken” cluster and practice fixing every security vulnerability manually.
Common mistakes
- Underestimating the importance of host-level security (Linux hardening).
- Forgetting to renew the CKA prerequisite before scheduling the CKS exam.
Best next certification after this
- Same-track option: Professional Cloud Security Engineer.
- Cross-track option: HashiCorp Certified Vault Associate.
- Leadership option: CISO certification path.
Choose Your Learning Path
DevOps Path
The DevOps path emphasizes the integration of security tools into the automation lifecycle. Engineers learn to treat security as code, ensuring that every deployment automatically meets the organization’s hardening standards. This path focuses on the balance between developer speed and infrastructure safety.
DevSecOps Path
Practitioners on this path focus entirely on the “Shift Left” philosophy of modern security. They implement automated scanning in CI/CD pipelines and use CKS techniques to block insecure code before it ever reaches the cluster. This is the most technically demanding path for security specialists.
SRE Path
Site Reliability Engineers treat security as a primary component of system uptime and reliability. They focus on the runtime monitoring and auditing aspects of the CKS curriculum. By detecting threats early, they ensure the cluster remains stable even under active attack.
AIOps Path
Engineers in the AIOps space use security telemetry to feed intelligent monitoring systems. They apply CKS auditing principles to generate the high-quality data needed for machine learning models. These models eventually help predict and prevent breaches before they occur.
MLOps Path
The MLOps path secures the specialized workloads used for training and deploying artificial intelligence models. Professionals ensure that sensitive datasets remain isolated within the cluster. They use CKS hardening techniques to protect GPU resources and model endpoints from unauthorized access.
DataOps Path
DataOps specialists apply CKS knowledge to secure data pipelines and persistent storage layers. They focus on encrypting data at rest and in transit within the Kubernetes environment. This path ensures that the data platform complies with global privacy regulations.
FinOps Path
The FinOps path ensures that cost-optimization strategies do not create new security vulnerabilities. For example, engineers learn to secure spot instances and audit the permissions of cost-tracking agents. This path aligns financial efficiency with a strong security posture.
Role → Recommended Certified Kubernetes Security Specialist (CKS) Certifications
| Role | Recommended Certifications |
| DevOps Engineer | CKA, CKS, KCNA |
| SRE | CKA, CKS, PCA |
| Platform Engineer | CKA, CKS, Terraform Associate |
| Cloud Engineer | CKA, CKS, Provider Security |
| Security Engineer | CKS, CISSP, CISA |
| Data Engineer | CKA, CKS, Data Specialty |
| FinOps Practitioner | KCNA, FinOps Practitioner |
| Engineering Manager | KCNA, CKA (Foundation) |
Next Certifications to Take After Certified Kubernetes Security Specialist (CKS) Certification Training Course
Same Track Progression
Deepen your expertise by pursuing advanced security credentials from major cloud providers like AWS, Azure, or GCP. These certifications complement your CKS knowledge by teaching you how to secure the managed services that surround your Kubernetes clusters. This combination makes you an expert in holistic cloud defense.
Cross-Track Expansion
Expand your architectural reach by mastering service mesh technologies like Istio or infrastructure automation with Terraform. These skills allow you to implement complex security features like mutual TLS and immutable infrastructure. This makes you a more versatile engineer capable of designing entire secure ecosystems from the ground up.
Leadership & Management Track
Transition into strategic roles by pursuing certifications like the CISM or PMP to complement your technical background. These credentials help you manage security teams and communicate technical risks to executive leadership. You will learn to align technical hardening efforts with the overall business objectives of your organization.
Training & Certification Support Providers for Certified Kubernetes Security Specialist (CKS) Certification Training Course
- DevOpsSchool: This prominent institution provides a deeply practical learning experience tailored for the CKS exam. Students benefit from an environment that simulates the actual performance-based test, allowing them to gain confidence before the real challenge. The trainers offer years of industry experience, ensuring that the lessons go beyond the basics into complex, real-world troubleshooting. Their support extends to personalized mentorship, which helps students navigate difficult security concepts like admission controllers and system-level hardening with ease.
- Cotocus: This provider excels in delivering specialized training modules for advanced cloud-native security practitioners. They focus on the specific tools mentioned in the CKS curriculum, such as Falco and Trivy, providing extensive lab time for each. Their approach suits working professionals who need to balance their learning with a full-time job, offering flexible schedules and high-quality recorded content. By choosing this provider, engineers gain access to a curriculum that remains strictly aligned with the latest CNCF exam standards.
- Scmgalaxy: This community-driven platform offers a wealth of resources for those pursuing Kubernetes certifications. It serves as an excellent hub for finding documentation, mock exams, and peer support during the preparation phase. Their CKS modules are designed to be accessible and clear, helping engineers break down complex security domains into manageable learning blocks. The site also provides regular updates on the latest trends in the DevOps and security landscape, keeping students informed and relevant.
- BestDevOps: This training provider focuses on high-impact, short-duration courses that help engineers upskill quickly. Their CKS program targets the core competencies required to pass the exam, making it an efficient choice for busy professionals. They offer a strong emphasis on lab-based learning, ensuring that students spend more time in the terminal than in theoretical lectures. Their instructors provide direct feedback on lab performance, helping candidates identify and fix their weak points before the exam day.
- devsecopsschool.com: This specialized school focuses exclusively on the integration of security into the DevOps lifecycle. Their CKS training program is part of a larger roadmap that teaches engineers how to build a complete “Shift Left” security culture. They emphasize the use of automation for security testing and the implementation of compliance-as-code. Students learn to handle real production threats, making them ready for immediate employment in high-level security roles within the tech industry.
- sreschool.com: This institution frames Kubernetes security through the lens of site reliability and system performance. Their CKS curriculum emphasizes the importance of monitoring, logging, and runtime protection for maintaining cluster health. Students learn how security incidents impact overall system reliability and how to mitigate those risks without causing downtime. This approach is perfect for SREs who want to add a strong security layer to their existing operational and troubleshooting skills.
- aiopsschool.com: This provider explores the future of infrastructure by combining artificial intelligence with Kubernetes security operations. Their training shows how to use CKS auditing data to feed intelligent anomaly detection systems. Students gain a unique perspective on how to automate threat response using machine learning models. This is an ideal choice for forward-thinking engineers who want to stay at the cutting edge of the tech landscape and the security industry.
- dataopsschool.com: This training center focuses on the specific security challenges of running large-scale data platforms on Kubernetes. Their CKS modules teach students how to protect data pipelines, secure persistent storage, and manage encrypted communication. They highlight the intersection of security and data privacy, preparing engineers for roles in highly regulated industries like finance and healthcare. The curriculum is practical and focuses on the high-value data assets that organizations need to protect.
- finopsschool.com: This organization teaches engineers how to align their security practices with financial optimization goals. Their CKS-related content shows how to securely manage cloud costs and audit the permissions of third-party optimization tools. Students learn to implement cost-saving measures without introducing new vulnerabilities into the cluster. This ensures that the organization remains both financially efficient and technically secure, providing a holistic view of modern cloud-native platform management and strategy.
Frequently Asked Questions
1. Can I attempt the CKS exam without a valid CKA certification?
No, the Linux Foundation requires you to hold a currently active CKA certification before you can officially take the CKS exam.
2. How long do I have to complete the CKS examination?
The exam lasts for two hours, during which you must complete a series of hands-on technical tasks in a command-line environment.
3. What is the minimum passing score required for the CKS?
You must achieve a score of at least 67% to successfully earn your Certified Kubernetes Security Specialist credential.
4. Does the exam use a multiple-choice format?
The CKS is entirely performance-based, meaning you solve real problems in a terminal rather than answering multiple-choice questions.
5. How many attempts do I get for the exam fee?
The standard exam purchase from the Linux Foundation includes one free retake if you fail your first attempt.
6. Which version of Kubernetes does the CKS exam currently target?
The exam usually tracks the most recent stable release of Kubernetes, typically updated every few months to stay current.
7. Are there any specific tools I need to study besides Kubernetes itself?
Yes, you must be proficient in using third-party tools like Falco, Trivy, and Kube-bench as they are core to the curriculum.
8. Can I use the official Kubernetes documentation during the test?
You are allowed to open one additional browser tab to access the official Kubernetes, Falco, and Trivy documentation pages.
9. How long does the CKS certification remain valid?
The certification remains valid for a period of two years, after which you must retake the exam to stay certified.
10. What is the best way to practice for the performance-based environment?
Using simulators like Killer.sh and setting up your own local clusters with Kubeadm provides the best hands-on preparation.
11. Is the CKS considered harder than the CKA exam?
Most practitioners consider the CKS more difficult because it introduces complex security concepts and multiple third-party open-source tools.
12. Will I need to know how to harden the Linux host operating system?
Yes, the exam includes tasks related to system-level hardening, such as configuring AppArmor, Seccomp, and kernel security modules.
FAQs on Certified Kubernetes Security Specialist (CKS) Certification Training Course
1. Which domains carry the most weight in the CKS examination?
The “System Hardening” and “Minimize Microservice Vulnerabilities” domains typically represent the largest portions of the exam score. Candidates must demonstrate proficiency in securing the host OS and isolating workloads using network policies and security contexts. Failing to master these areas often leads to a failing grade, so practitioners should dedicate significant lab time to these specific tasks.
2. How do I practice for the runtime security monitoring tasks?
Runtime security practice involves setting up tools like Falco to detect suspicious activities such as unauthorized shell executions or file modifications. You should learn to write custom Falco rules and interpret the generated logs to identify potential breaches. This skill is critical for the exam, as you will likely need to configure monitoring to catch specific malicious behaviors in a live cluster.
3. What role does image scanning play in the CKS curriculum?
Image scanning is a fundamental skill that requires you to use tools like Trivy to identify vulnerabilities in container images. The exam may ask you to scan images and block deployments that contain high-severity flaws. This process ensures that you can protect the software supply chain by preventing insecure code from ever running in your production environment.
4. Can you explain the importance of the Open Policy Agent (OPA) in this course?
OPA Gatekeeper acts as a powerful admission controller that allows you to enforce custom policies on your cluster resources. In the CKS, you learn to use OPA to ensure that all pods meet specific security standards, such as requiring a read-only root filesystem. Mastering OPA allows you to automate compliance and prevent misconfigurations across the entire organization.
5. How does the exam test knowledge of the Kubernetes API server?
The exam often requires you to harden the API server by disabling insecure ports and enabling specific admission controllers. You might also need to configure auditing to log every request made to the API, providing a clear trail for security forensics. Understanding the various flags and configuration options for the API server is essential for securing the control plane.
6. Will I need to manage secrets and encryption at rest?
Yes, the CKS curriculum includes tasks related to the secure management of Kubernetes Secrets and the implementation of encryption providers. You must know how to encrypt sensitive data in etcd and how to restrict access to secrets using RBAC. These tasks ensure that even if an attacker gains partial access to the cluster, they cannot easily steal credentials.
7. What is the best strategy for managing time during the two-hour exam?
Experienced engineers suggest skipping extremely difficult or time-consuming tasks and returning to them after completing the easier ones. Using imperative kubectl commands instead of writing long YAML files from scratch saves valuable minutes. Proper time management is often the deciding factor between passing and failing this high-pressure, performance-based assessment.
8. How do I stay updated with changes to the CKS exam syllabus?
The CNCF regularly updates the syllabus, and you should follow their official GitHub repository and website for the latest announcements. Training providers like DevOpsSchool also update their materials to reflect these changes, ensuring that students aren’t studying outdated tools or techniques. Keeping an eye on community forums and blogs can also provide insights into recent exam shifts.
Final Thoughts: Is Certified Kubernetes Security Specialist (CKS) Certification Training Course Worth It?
Investing in the CKS certification provides a clear competitive advantage in an increasingly crowded cloud-native job market. It transforms a standard administrator into a security specialist who can design and defend enterprise-grade infrastructure against sophisticated attacks. For any engineer looking to future-proof their career, the depth of knowledge gained during this training is far more valuable than the certificate itself.
Choosing to master these skills demonstrates a commitment to the highest standards of professional excellence and infrastructure reliability. As Kubernetes continues to dominate the enterprise landscape, the need for certified defenders will only grow, making this one of the most stable career paths in technology. If you possess the CKA and have a passion for high-stakes problem solving, this certification represents the logical and highly rewarding next step in your professional journey.